Continue reading to learn more about PKI and its use in securing file transfers.
How Does PKI Work?
PKI uses asymmetric encryption methods to protect data and authenticate the sender. In asymmetric encryption there are two keys: one public and one private. Anyone can see the public key, but the private key is only known to the recipient. The private key must remain private so that only the true recipient can decrypt the message. If others can access and use the private key, the data is no longer secure.
How Does PKI Work in Transferring Files?
Here’s how PKI works at a very high level:
- Bob wants to send data to Alice. He uses his public key to encrypt (or make unreadable) the file.
- The file is transferred to Alice.
- Alice receives the file and uses her private key to decrypt (or make readable) the file.
Get Complete File Transfer Security with MFT
The most secure way to exchange files is to use a managed file transfer (MFT) solution that protects files with end-to-end encryption (E2EE), including encrypting files at rest. Thru’s automated MFT service includes built-in support for three commonly used secure protocols: SFTP, FTPS and HTTPS.
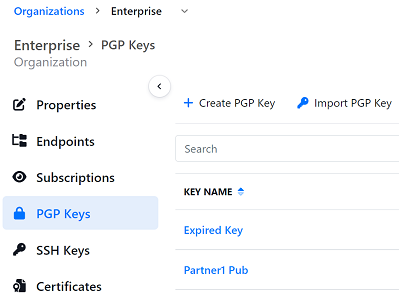
Thru’s web-based interface allows you to manage your keys or certificates:
- Create or import SSH keys to be used with SFTP endpoints.
- Import SSL client certificates for FTPS endpoints.
- Create or import PGP (Pretty Good Privacy) keys for file-level encryption. PGP signing also available.
Learn more about how Thru secures file transfers »
